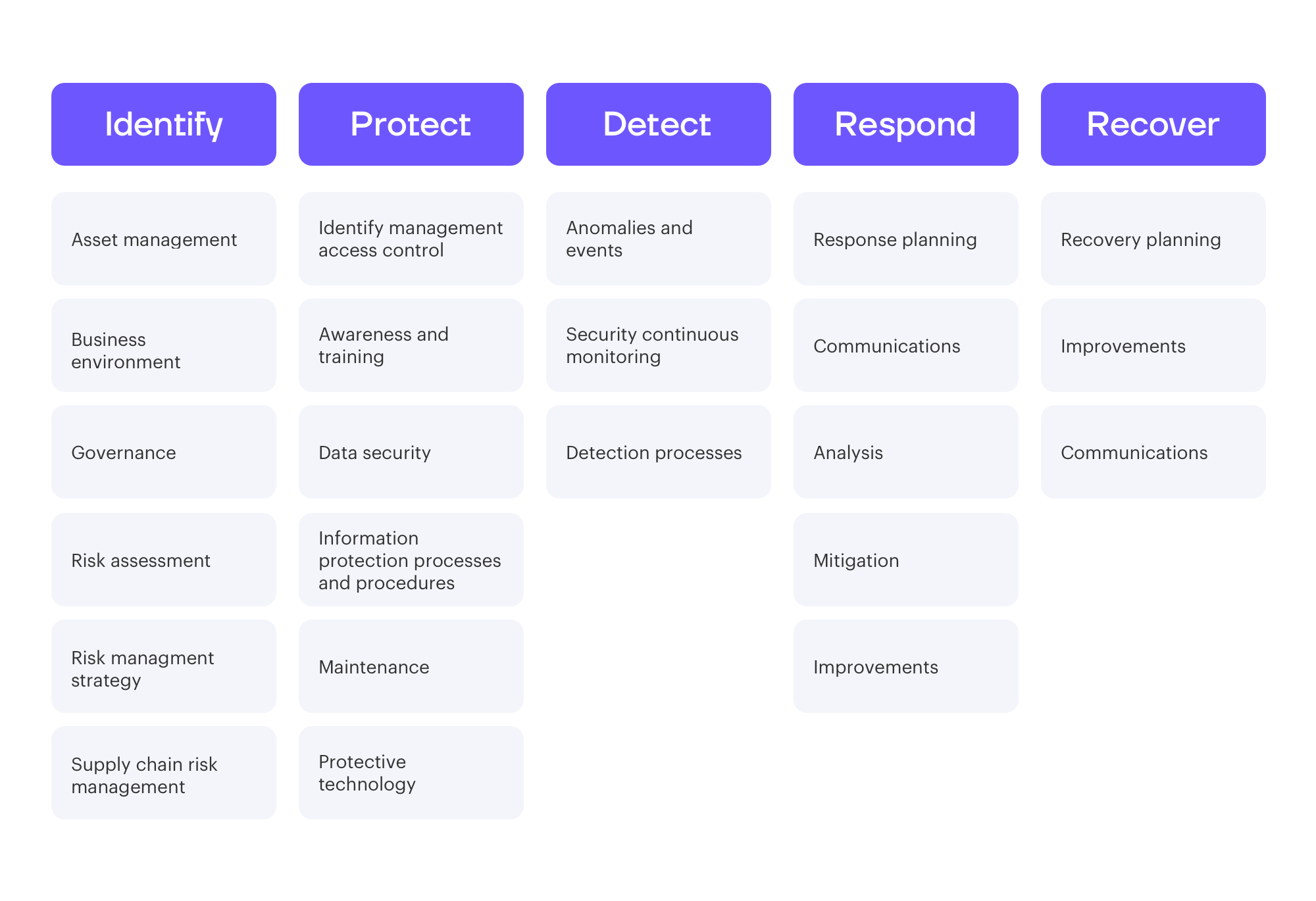
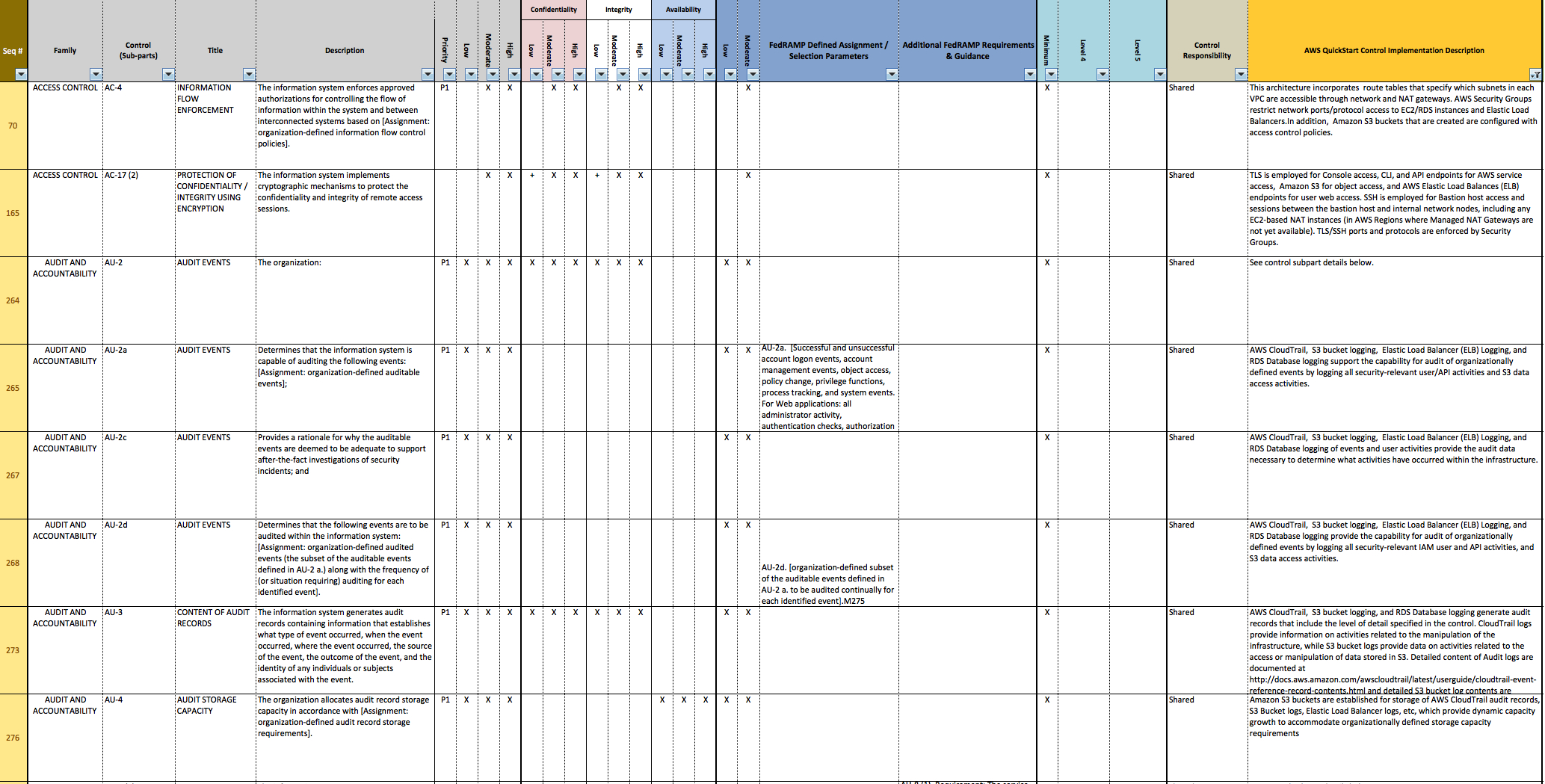
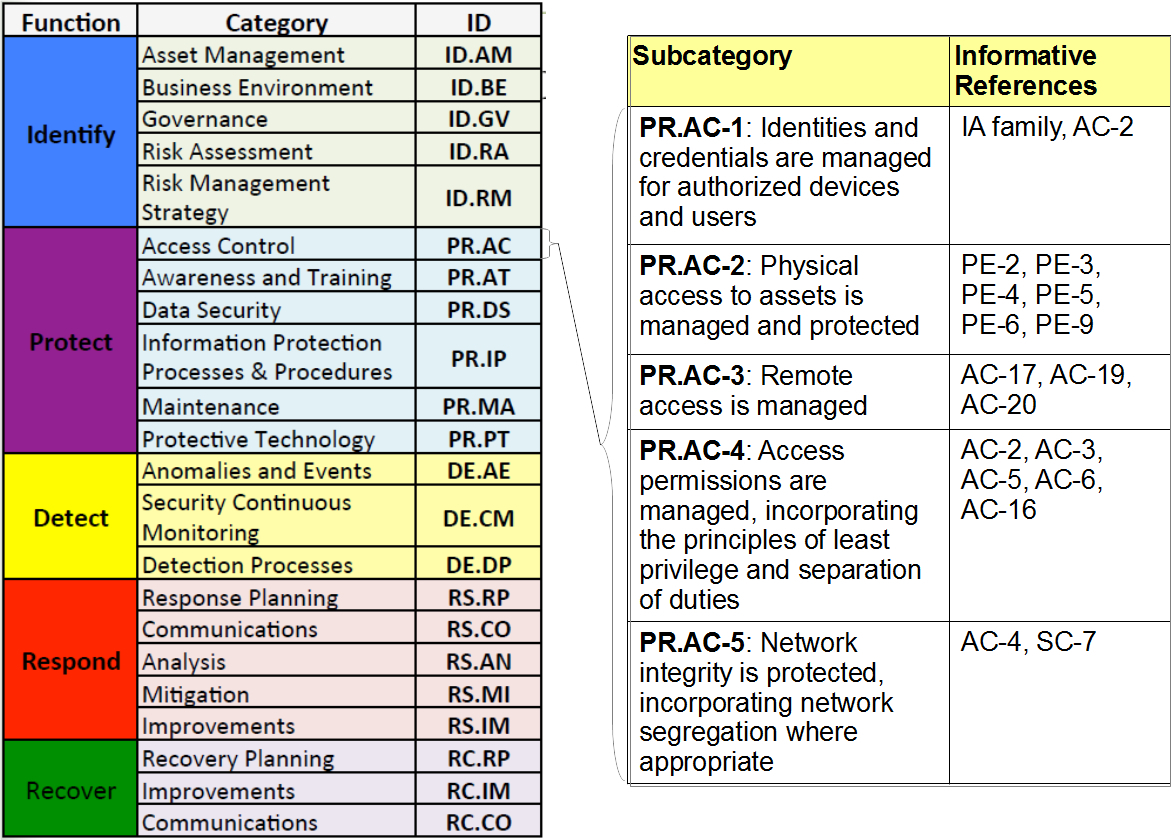
Nist 800 53 Template - Security and privacy controls for information systems and organizations. Simply put, if you run support or “supply chain” operation, the defense federal acquisition regulation supplement (dfars) made specific cybersecurity protocols a requirement. 2 the threat brief recommended several protective measures to. Vulnerability & patch management program. Federal information systems typically must go through a formal assessment and authorization process to ensure sufficient protection of confidentiality, integrity, and availability of information and information. By establishing a framework available to all, it fosters communication and allows organizations to speak using a shared language. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. Target audience (community) comments point of contact informative reference submission form dependency/ requirement field name reference version Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program collaboration to help ensure that the objectives of both disciplines are met and that risks are appropriately managed. Web this publication provides a catalog of security and privacy controls for federal information systems and organizations and a process for selecting controls to protect organizational operations (including mission, functions, image, and reputation), organizational assets, individuals, other organizations, and the nation from a diverse set.
Nist Sp 800 53 Rev 4 Spreadsheet —
This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. This publication is available free of charge from: Vulnerability & patch management program. Simply put, if you run support or “supply chain” operation, the defense federal acquisition regulation supplement (dfars) made specific cybersecurity protocols a requirement. 2 the threat brief recommended several.
Nist 800 53 Risk Assessment Template Master of Documents
The publication itself states it. Web this publication provides a catalog of security and privacy controls for federal information systems and organizations and a process for selecting controls to protect organizational operations (including mission, functions, image, and reputation), organizational assets, individuals, other organizations, and the nation from a diverse set. Web last year, the department of health and human services’.
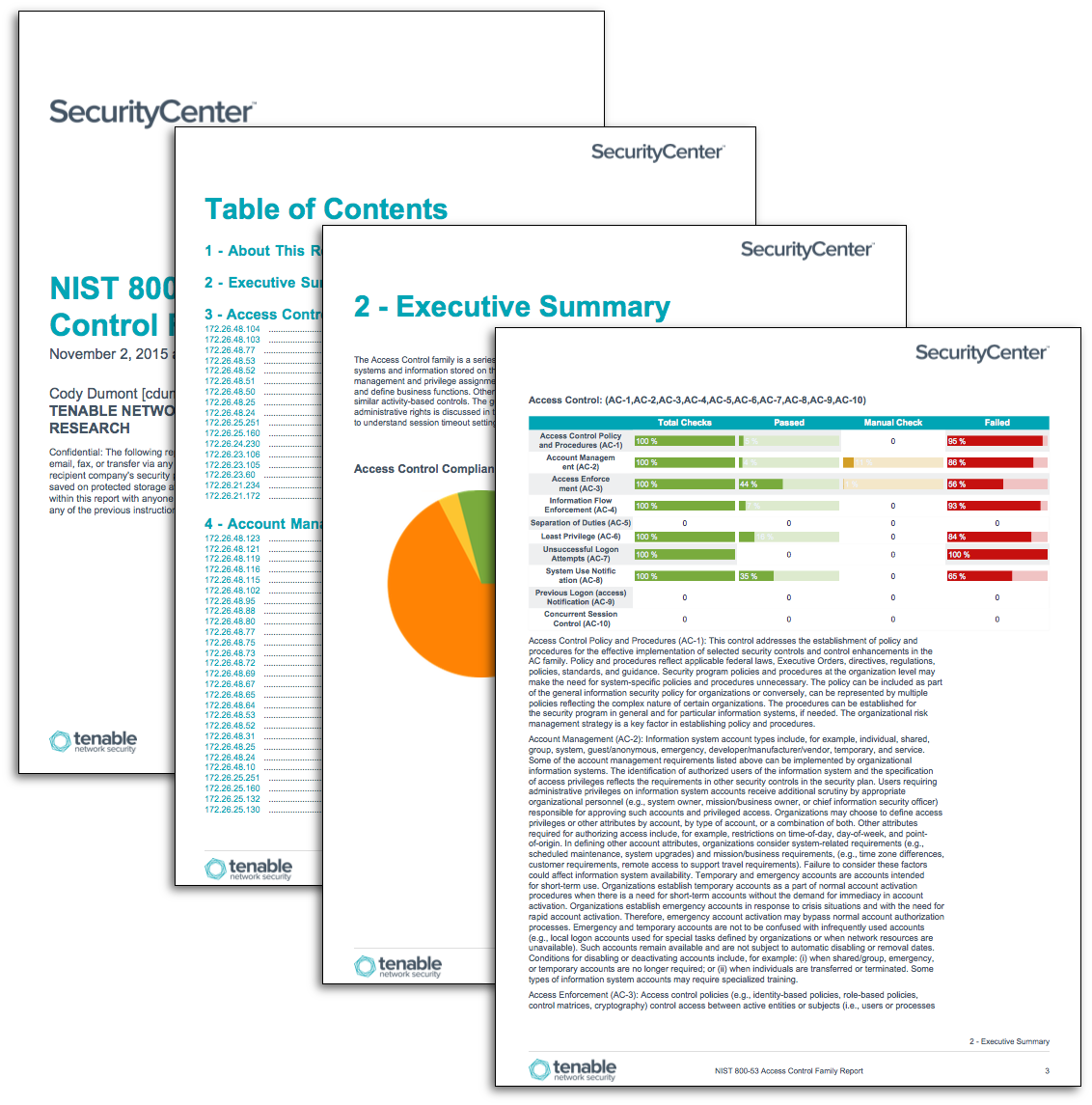
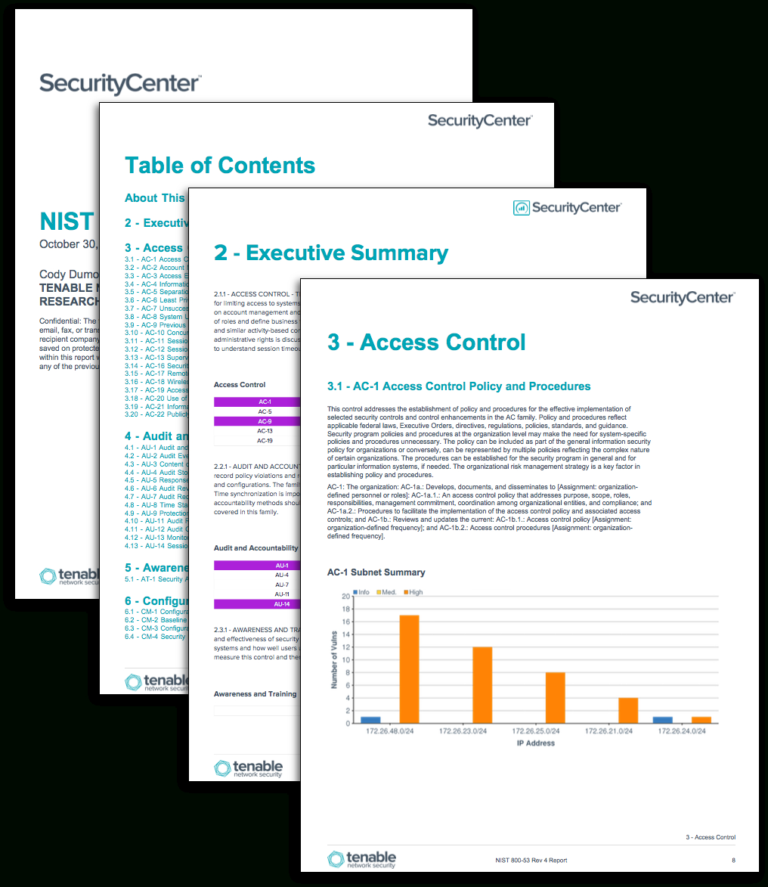
NIST 80053 Family Reports SC Report Template Tenable®
Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program collaboration to help ensure that the objectives of both disciplines are met and that risks are appropriately managed. Web 0 1 2 3 4 5 6 7 8 9 10. By establishing a framework available to all, it.
Nist 800 53 Rev 5 Controls Spreadsheet —
Security and privacy controls for information systems and organizations. Risk assessment csf v1.1 references: Web this publication provides a catalog of security and privacy controls for federal information systems and organizations and a process for selecting controls to protect organizational operations (including mission, functions, image, and reputation), organizational assets, individuals, other organizations, and the nation from a diverse set. Federal.
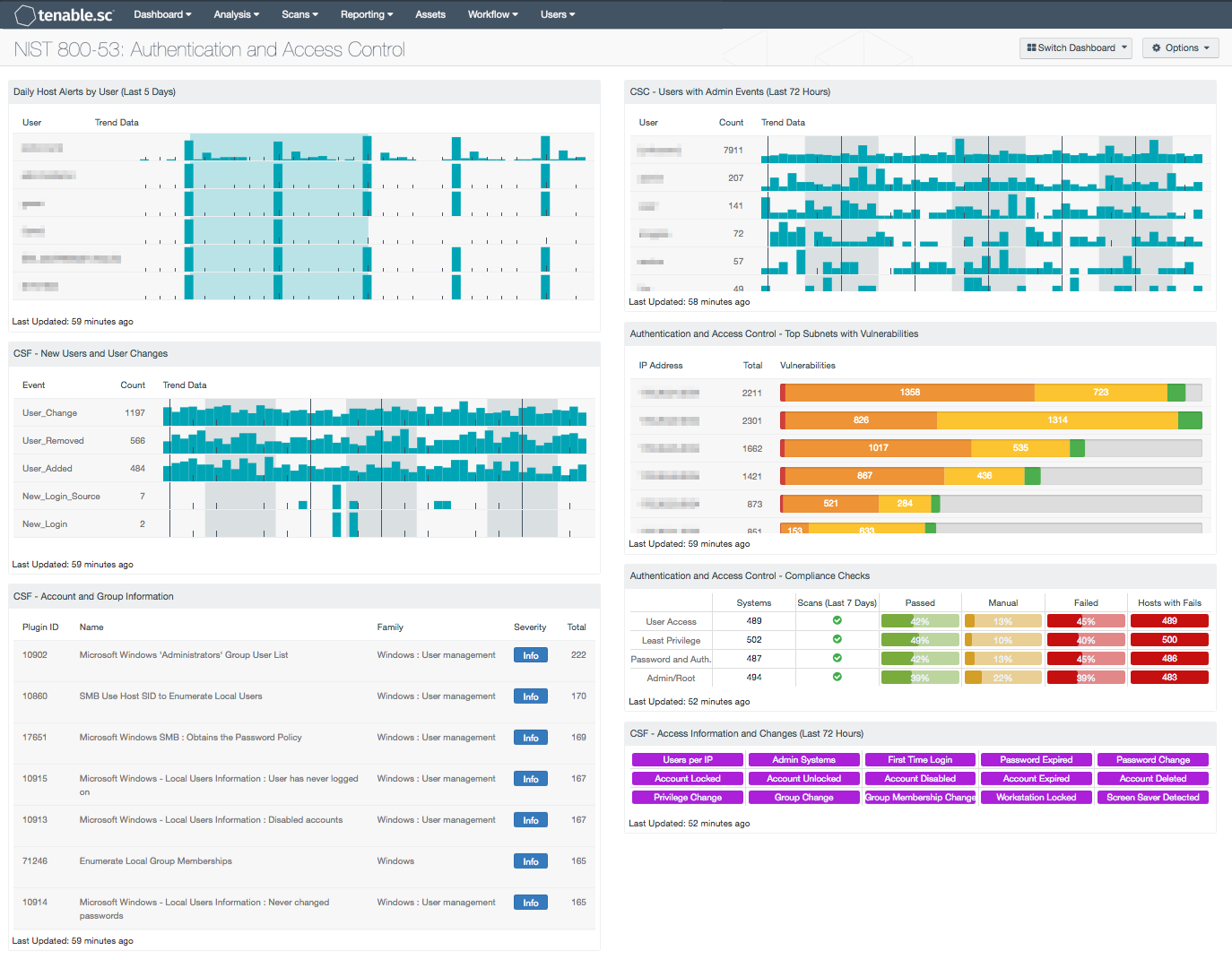
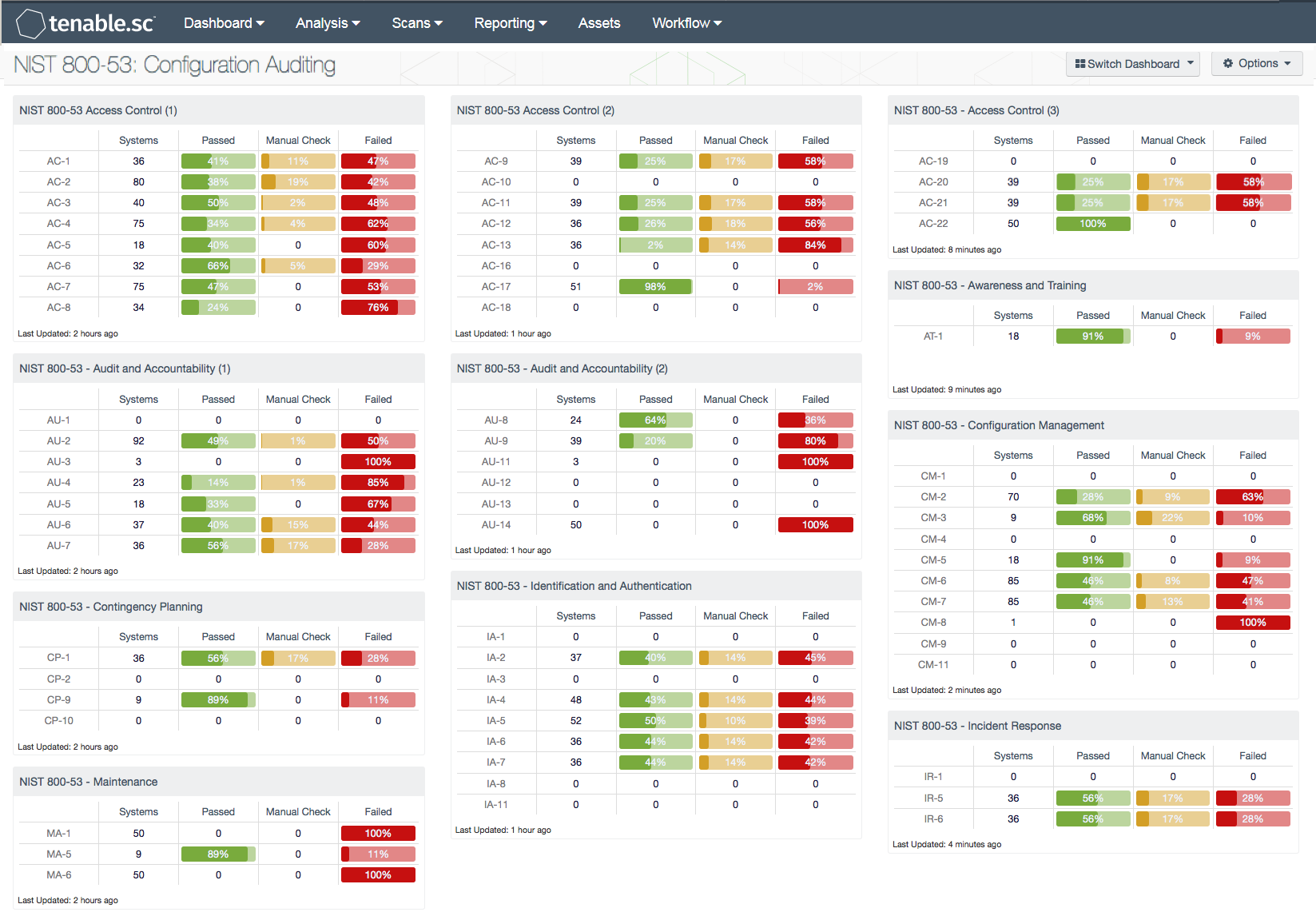
NIST 80053 Authentication and Access Control SC Dashboard Tenable®
Web 0 1 2 3 4 5 6 7 8 9 10. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. Risk assessment csf v1.1 references: Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program collaboration to help.
NIST 80053 rev. 5 compliance Qush blog
2 the threat brief recommended several protective measures to. Security and privacy controls for information systems and organizations. Prior to the 2.4 branch, a template functionality which allows users to create templates allows them to execute any code on the server during the bad filtration and old twig version. This publication is available free of charge from: Risk assessment csf.

Nist Sp 800 53 Rev 4 Spreadsheet Spreadsheet business, Business
Web joint task force abstract this publication provides a methodology and set of procedures for conducting assessments of security and privacy controls employed within systems and organizations within an effective risk management framework. Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program collaboration to help ensure that.
Nist 800 53 Security Controls Spreadsheet Google Spreadshee nist 80053
Web 0 1 2 3 4 5 6 7 8 9 10. By establishing a framework available to all, it fosters communication and allows organizations to speak using a shared language. Vulnerability & patch management program. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. Federal information systems typically must go.
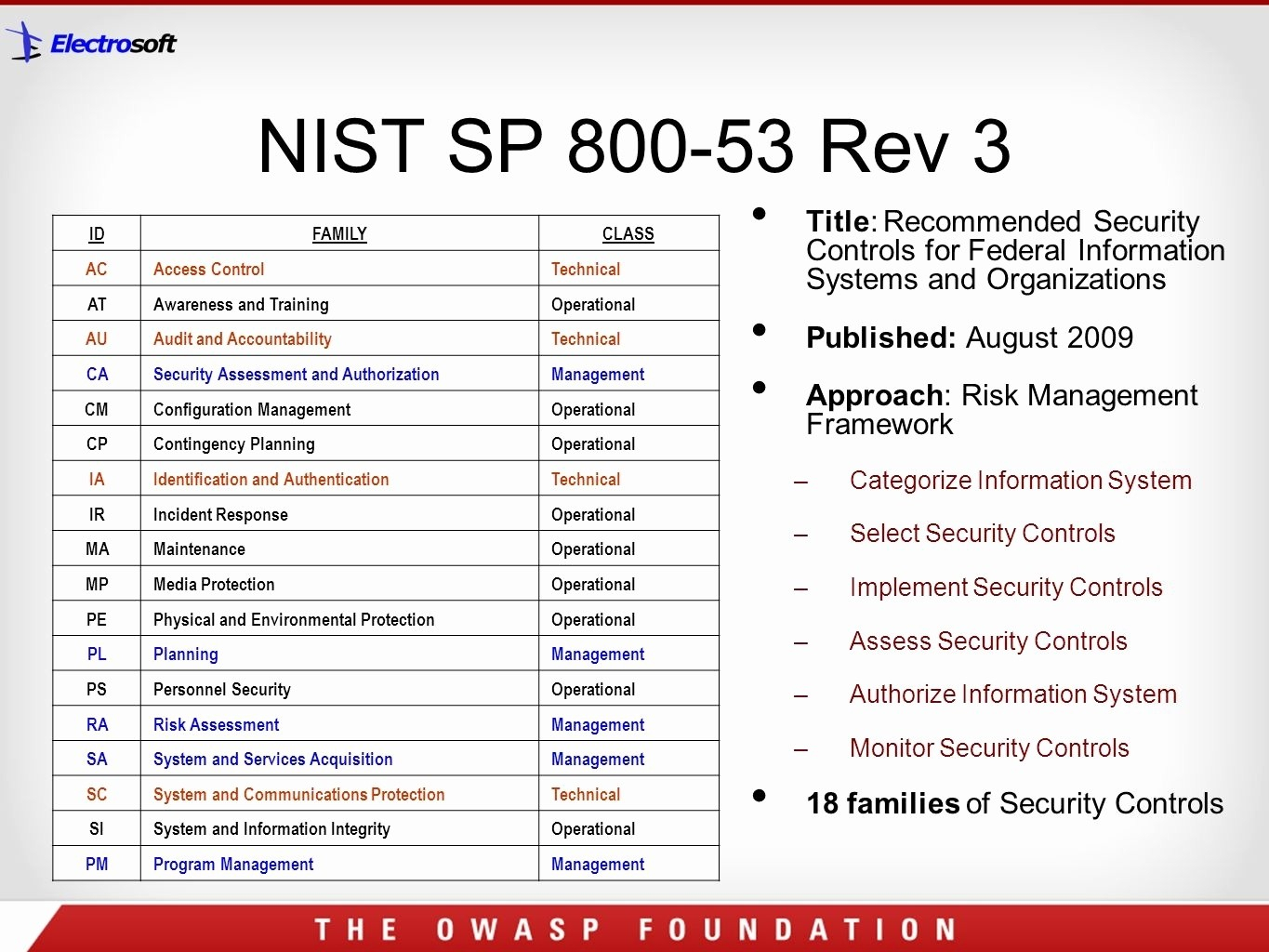
Nist 800 53 Rev 3 Spreadsheet —
2 the threat brief recommended several protective measures to. Simply put, if you run support or “supply chain” operation, the defense federal acquisition regulation supplement (dfars) made specific cybersecurity protocols a requirement. Web 0 1 2 3 4 5 6 7 8 9 10. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and.

Nist 800 53 Risk Assessment Template Free Printable Template
Simply put, if you run support or “supply chain” operation, the defense federal acquisition regulation supplement (dfars) made specific cybersecurity protocols a requirement. Risk assessment csf v1.1 references: Web joint task force abstract this publication provides a methodology and set of procedures for conducting assessments of security and privacy controls employed within systems and organizations within an effective risk management.
Security and privacy controls for information systems and organizations. Federal information systems typically must go through a formal assessment and authorization process to ensure sufficient protection of confidentiality, integrity, and availability of information and information. 2 the threat brief recommended several protective measures to. Vulnerability & patch management program. Web 0 1 2 3 4 5 6 7 8 9 10. Prior to the 2.4 branch, a template functionality which allows users to create templates allows them to execute any code on the server during the bad filtration and old twig version. Risk assessment csf v1.1 references: Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program collaboration to help ensure that the objectives of both disciplines are met and that risks are appropriately managed. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. Target audience (community) comments point of contact informative reference submission form dependency/ requirement field name reference version Web the ncsr question set represents the national institute of standards and technology cybersecurity framework (nist csf). Web this publication provides a catalog of security and privacy controls for federal information systems and organizations and a process for selecting controls to protect organizational operations (including mission, functions, image, and reputation), organizational assets, individuals, other organizations, and the nation from a diverse set. Web last year, the department of health and human services’ (hhs) health sector cybersecurity coordination center (hc3) released a threat brief on the different types of social engineering 1 that hackers use to gain access to healthcare information systems and data. By establishing a framework available to all, it fosters communication and allows organizations to speak using a shared language. Simply put, if you run support or “supply chain” operation, the defense federal acquisition regulation supplement (dfars) made specific cybersecurity protocols a requirement. The publication itself states it. Web joint task force abstract this publication provides a methodology and set of procedures for conducting assessments of security and privacy controls employed within systems and organizations within an effective risk management framework. This publication is available free of charge from: